
03) Does your organisation conduct a business impact assessment for each supplier and give them a corresponding criticality rating?
Answer yes if your organisation assigns each supplier with a criticality rating that is based on a corresponding business impact assessment.
Supply chain security is the process through which companies assess the security of their suppliers and gain assurance that they are secure enough to enter into business with.
The process is split into two parts. The first part is a criticality assessment of each supplier which is done internally within the client company. This is usually done using a Business Impact Assessment (or BIA). This prioritises the suppliers and defines the level of controls that the supplier has to have implemented before data can be shared with them. The criticality assessment can be thought of as defining the ‘impact’ component of the risk of the supplier undergoing a security breach.
The second part is the security review of each supplier (controls I4, I5, and I6). This consists of engaging the supplier to complete a security assessment and then the subsequent marking of the assessment to gain comfort that the supplier has implemented an appropriate level of security controls. The security assessment can be thought of as the ‘probability’ component of the risk of the supplier undergoing a security breach - the more security controls a supplier has, the lower the probability of a breach.
Assessing Criticality
Assessing the criticality of a supplier is essentially determining how important a supplier is to your company. The key question to ask is how big of an impact would a breach of confidentiality or availability of service at a supplier impact your own business?
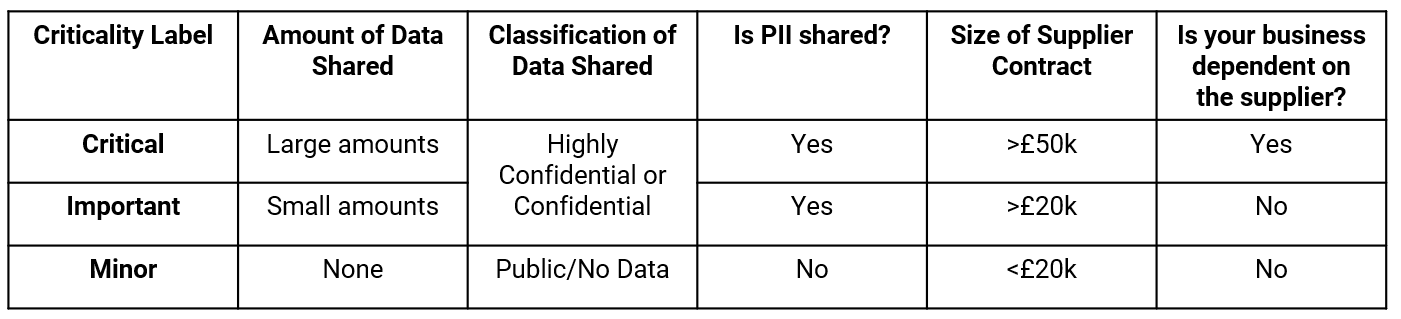
Typically, to help us answer this question we use certain parameters to assess that impact, such as:
- Amount and classification of data shared with supplier;
- Amount of PII shared with the supplier;
- Size of financial contract with the supplier;
- Dependence of your business on the suppliers service.
Once we have answers to the above questions we then assign a criticality label to the supplier – either Critical, Important, or Minor. The thresholds that determine which supplier is assigned which label vary by company but we have provided an example below.
How to implement the control
In order to implement this control you need to do the following:
- Identify who all of your businesses suppliers are;
- Conduct a business impact assessment using the above questions against each;
- Assign each a criticality label.
You then need to integrate the above process into your standard procurement cycle to ensure all newly procured suppliers moving forward have a business impact assessment completed and are categorised by their criticality.
If you are a larger organisation you may need some external consulting help to complete this work.
If you would like to contribute to this article or provide feedback, please email knowledge@riskledger.com. Contributors will be recognised on our contributors page.


.svg)