Have you invested heavily in your TPRM engine, followed every TPRM best practice, and nailed every compliance audit, but still remain exposed to supply chain breaches?
You’re not alone. Only 37.2% of UK cyber security professionals consider Third-Party Risk Management (TPRM) "truly effective” for today’s threats. But TPRM defences aren't failing through lack of effort or insufficient budget. They’re failing because TPRM software was built for compliance in a disconnected world, not resilience in a connected one.
From static assessments to limited network visibility, TPRM’s limitations are unfixable structural failures. That’s why organisations are moving beyond TPRM towards Active Supply Chain Security (ASCS), a new operating model for supply chain security built on continuous visibility, shared intelligence, and systemic risk reduction across the entire supply chain ecosystem.
Rather than comparing tools, this comparison reflects the shift from traditional assurance models toward a more connected and continuous supply chain security approach.
TPRM vs ASCS: Assessing supplier security
Third-Party Risk Management (TPRM): Traditional TPRM relies on periodic supplier risk assessments. Each organisation creates a questionnaire, shares it with a prospective supplier and reviews the responses in order to assess the supplier’s security posture. This process leads to:
- Never-ending questionnaires. Every time a global security regulation changes, a new attack method surfaces or network breach comes to light, security analysts must research the issue, manually update the questionnaire, and re-share with suppliers, leading to hours of duplicated effort.
- Incomparable responses. Every supplier fills in security questionnaires in a different way, making it impossible to compare security postures and risk levels across a diverse supply chain.
- Inaccurate answers. With lots of nearly identical but technically distinct questionnaires to fill in, suppliers rush responses and "copy-paste" answers leading to errors.
vs
Active Supply Chain Security (ASCS): ASCS relies on standardised risk assessments. Organisations use one assessment (aligned with relevant security regulations), while suppliers create, maintain and share just one security profile with all clients. This process leads to:
- One common language of risk. The entire ecosystem uses the same language to describe risk, enabling efficient security reviews, simplified due diligence and streamlined regulatory reporting.
- Up-to-date risk profiles. As suppliers maintain a single, standardised security profile, you access up-to-date, consistent and peer-validated supplier assessments at any time.
- Streamlined supplier onboarding. Instead of endlessly chasing suppliers, you assess suppliers instantly with pre-built workflows and processes — reducing onboarding time by over 50%.
TPRM vs ASCS: Supply chain visibility and risk monitoring
Third-Party Risk Management (TPRM): Traditional TPRM focuses on direct, third-party suppliers. Each organisation vets its immediate partners in isolation and creates a linear list of compliant suppliers, which requires manual updates when a supplier’s security posture changes. This process leads to:
- Unseen nth party threats. This narrow focus fails to identify your suppliers’ suppliers - be they SaaS products, data storage providers, or cloud services - leaving you blind to nth party risk deep in your supply chain.
- Unaware of concentration risks. Without full network visibility and live tracking of changing supplier relationships, you cannot see hidden dependencies (i.e. if all of your critical vendors rely on the same data centre), let alone manage them.
- Unprepared for cascading breaches. Be it attackers targeting a weak nth party or a security breach at a critical fourth-party, you are powerless to predict or prevent the cascading house of cards effect from flowing to you.
vs
Active Supply Chain Security (ASCS): ASCS maps your entire supply chain ecosystem to the nth degree. Each organisation can visualise their interconnected supply network in real-time, showing constantly updated nth-party connections. This process leads to:
- Nth‑party visibility. With the full picture of your 3rd, 4th and nth tier connections, you can proactively uncover shared dependencies and vulnerabilities.
- Concentration risk insights. With a bird's-eye view of your entire network, you can spot concentration risks and make plans to mitigate sudden disruptions (i.e. sanctions or policy changes).
- Network‑first defence. With thousands of organisations sharing intelligence, you can collectively plan for breaches and take action to avoid cascading failures before they happen.
TPRM vs ASCS: Detecting and monitoring emerging threats
Third-Party Risk Management (TPRM): Traditional TPRM identifies risks periodically. Each organisation requests assessment updates from its third-party suppliers (often on an annual basis) and updates a static document sitting in a procurement database. This process leads to:
- Instantly outdated risk data. Point-in-time questionnaires are outdated the very next day. If you only demand questionnaires on an annual basis, you’re blind to any changes in your suppliers’ security for 364 days of the year.
- Compliance-based security. Assessments are set up to satisfy audit requirements, not live security requirements. Even if all your third-party suppliers are compliant, you’re still vulnerable.
- Reliance on suppliers. Your entire supply chain security is based on suppliers actively and accurately updating their assessments, which takes control of your defences out of your hands.
vs
Active Supply Chain Security (ASCS): ASCS enables real-time threat visibility across interconnected supply chains. Each organisation on the network receives alerts to new vulnerabilities, emerging threats and real-time attacks, enabling time for proactive remediation. This process leads to:
- Continuous oversight. With constant updates on changing supplier risk, including cyber security incidents or compliance lapses, you can take premeditated action.
- Informed risk assessments. With real-time risk signals, intuitive dashboards and simulated disruptions, you can assess the impact of potential threats, create solid response playbooks and make informed choices around supplier diversification.
- Proactive threat management. By pinpointing emerging threats and potential vulnerabilities, you have time to execute your response plans and get ahead of incidents before they escalate.
TPRM vs ASCS: Managing supply chain security breaches
Third-Party Risk Management (TPRM): Traditional TPRM prioritises self-preservation. Each organisation defends their own IT perimeter alone, relying on organisation-gathered intelligence. This process leads to:
- Reactive firefighting. Without frictionless supplier engagement, you only find out about breaches when they’re at your door - by which time you’re already on the back foot.
- Independent defence. When a network breach occurs, your security team is fighting the exact same problem at the exact same time as your supply chain partners, but with no way of sharing intelligence or the burden.
- Short-sighted security. Even if you defend the breach successfully, the disruption will affect your entire supply chain partners and impact your business production in the future.
vs
Active Supply Chain Security (ASCS): ASCS prioritises ecosystem resilience. Each organisation seamlessly collaborates with security professionals in the network and shares intelligence between network partners. This process leads to:
- Proactive incident response. By leveraging network-level insights, ecosystem mapping and emerging threat detection, your whole industry moves from reactive firefighting to proactive threat mitigation.
- Collective defence. By creating a connected community of industry peers, you share intelligence and actively fight breaches together.
- Defend-as-one. With your security team working together with industry counterparts, you optimise the entire ecosystem's resources, reduce systemic risk across the ecosystem and ensure every link in the chain is fortified.
How Risk Ledger is shifting TPRM to ASCS
The direction of travel is clear: organisations are moving beyond traditional TPRM toward Active Supply Chain Security.
At Risk Ledger, we know that traditional TPRM leads to wasted effort and weakened defence. That’s why we’re helping define and advance the shift toward Active Supply Chain Security.
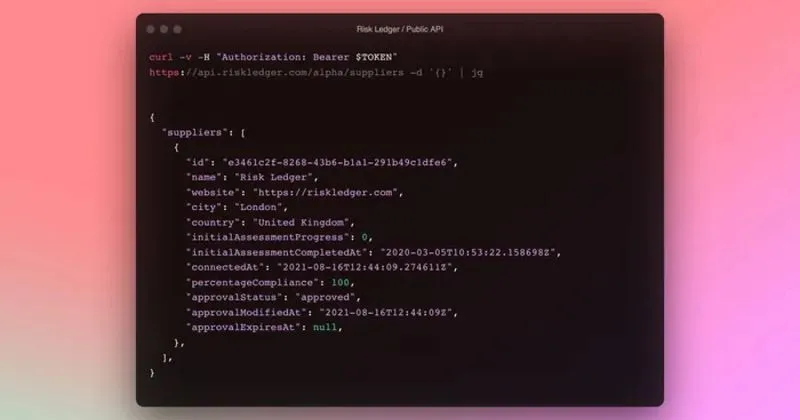
By standardising supplier data, connecting thousands of organisations onto a living network, and overlaying proactive threat intelligence, our four-stage approach is helping organisations move beyond fragmented TPRM toward a more connected, continuous supply chain security framework.






.svg)