.png)
How It Works
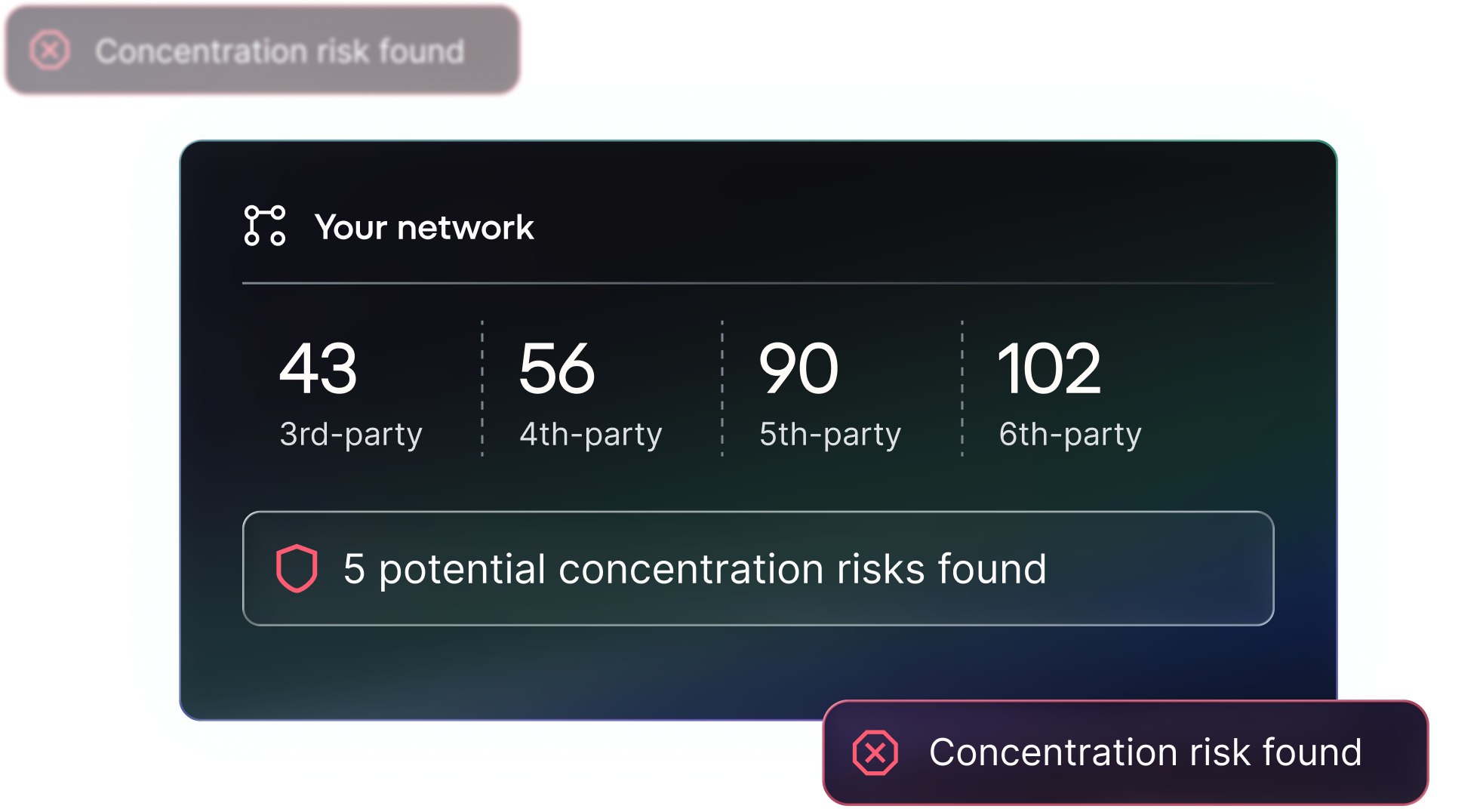
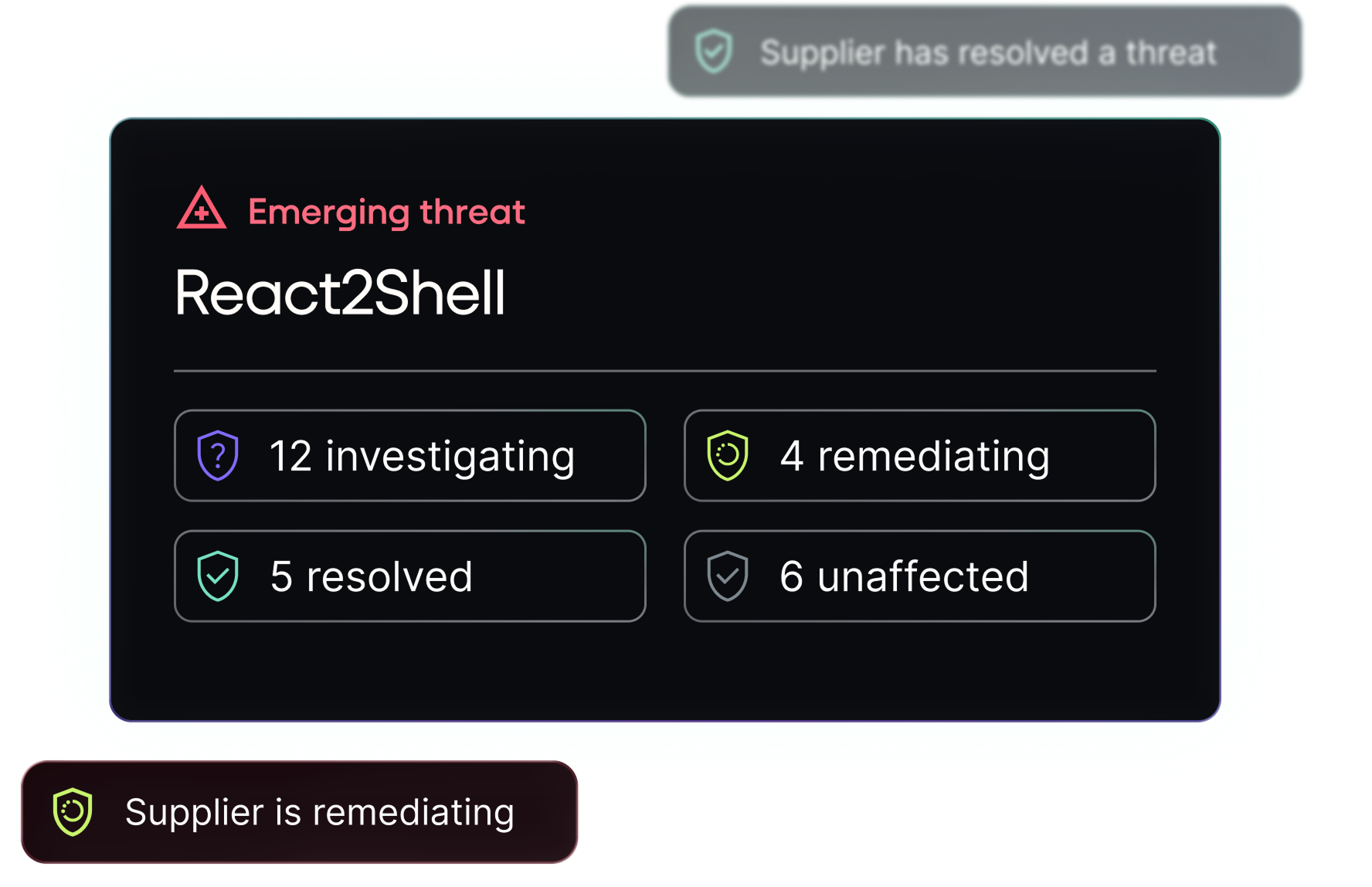
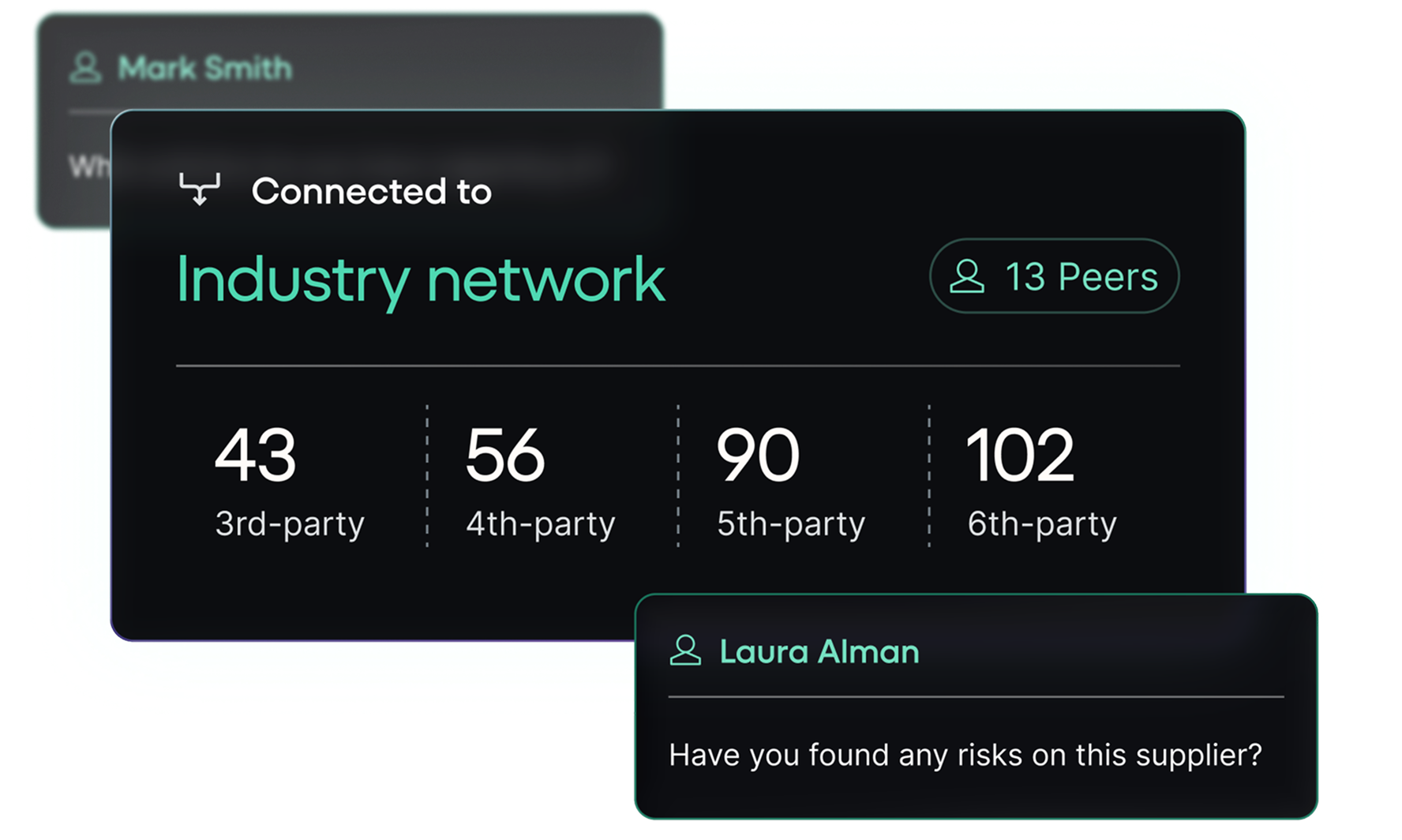
By standardising supplier data, mapping thousands of organisations onto a living network, overlaying emerging threats and allowing you to work with peers to build community resilience. Risk Ledger’s four-stage approach is transforming fragmented TPRM into Active Supply Chain Security.

.svg)