How we make it easy to comply with EBA guidelines and DORA
Risk Ledger makes identifying, monitoring, assessing and managing third party risk a simple and streamlined process.


With the rise of technology and the growing demand for digital solutions among both consumers and businesses, the lines between traditional finance and Fintech have blurred. Even those financial institutions still offering a largely traditional service to their clients are likely making use of cloud and other digital solutions as part of their daily operations.
As financial organisations, from banks and investment firms to payment and electronic money institutions, have shifted to outsourcing cloud and other managed ICT services, third party risk management has never been more critical. In light of this shift, the European Banking Authority (EBA) introduced guidelines on outsourcing in 2019 to establish an industry standard governance framework. Similarly, the European Union submitted draft legislation known as the Digital Operations Resilience Act (DORA) in 2020 to govern how financial organisations handle ICT risks.
Read on for a summary of what financial organisations need to do to comply and how Risk Ledger can help.\
By introducing their outsourcing guidelines, the EBA’s intention is to support innovation within financial services – while also minimising risk. This means that you now face the challenge of staying agile and competitive in fast-moving markets, while navigating the administrative and practical hurdles of complying with guidelines that require you to “identify, assess, monitor and manage all risks resulting from arrangements with third parties”.
The EBA’s outsourcing guidelines require you to identify concentration risk and critical dependencies between your third party suppliers. Risk Ledger makes this simple by giving you live access to a personalised network graph that maps:
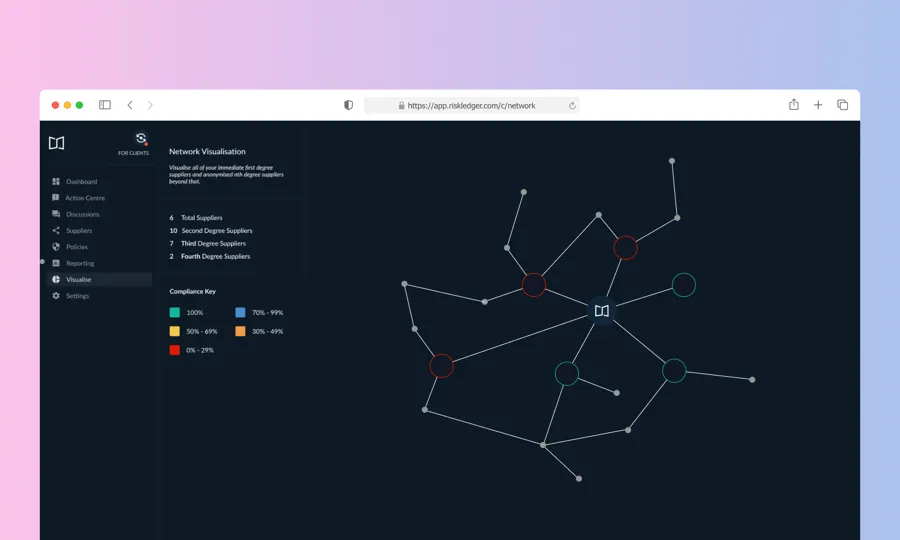
This kind of mapping has historically been incredibly difficult (if not impossible) but Risk Ledger’s social network model means you have visibility of your entire supply chain well beyond just third party connections and through to fourth, fifth and sixth parties.
Most third party risk management processes are built around point-in-time assessments which quickly go out of date. Risk Ledger solves this by making it easy for third parties to update their supplier profile when anything changes. With a Risk Ledger client account, you have access to an activity feed of all the changes your suppliers make to their security practices over time.
Because many third parties use their Risk Ledger supplier profile to manage security controls internally, you get a clear view inside your suppliers – lifting the lid on security controls, instead of taking the information you’re given at face value.\
Due to be finalised in 2022, the EU Digital Operations Resilience Act (DORA) will govern how financial organisations manage third party ICT risk. Put simply, DORA is being introduced to ensure that you can continue operating – even in the midst of a cyber attack. In order to comply with the DORA’s requirements, you’ll need to consider five key pillars:
It is this fifth pillar, ICT third party risk management, where you and your suppliers can use Risk Ledger to your shared advantage.
DORA applies to both financial organisations and their critical ICT suppliers, so it goes without saying that you’ll have to work together to ensure operations can continue uninterrupted during a supply chain attack or third party breach. The first step, then, is to identify which of your ICT suppliers are critical – a hassle-free process through Risk Ledger’s simple tagging and reporting functionality.
Through detailed control-based information available within Risk Ledger, you can easily identify where your critical ICT suppliers may have vulnerabilities and then use that knowledge to work with them on strengthening their defences (or to inform your decision to find an alternative provider).
Risk Ledger is free to suppliers, giving them access to a shareable profile they can use to breeze through security questionnaires. This means that the onboarding process and continued tracking of security controls over time is painless for everyone involved. By helping you and your critical ICT suppliers collaborate, Risk Ledger makes the shared responsibility of complying with DORA a lot less daunting.
It’s important to remember that by focussing mainly on your critical ICT suppliers, you expose your organisation to a whole host of risks lurking further down your supply chain. Suppliers who may not be critical on a third party level, for example, might have fourth party connections with your critical ICT suppliers that would have a serious knock-on effect that disrupts operations.
With Risk Ledger, you have unprecedented visibility of your entire supply chain, mapping every connection in your supplier network and uncovering risks you may not otherwise have noticed until an attack was already underway.\
As a financial organisation, having to comply with existing and evolving regulations can certainly slow down digital adoption and innovation – but it shouldn’t halt your progress altogether. Get in touch today to learn more about how Risk Ledger can simplify and streamline your third party risk management so you can focus on the future.
The EBA guidelines on outsourcing provide a framework for financial institutions to ensure effective day-to-day management and oversight, proper identification of critical or important functions, and suitability of potential service providers. These EBA outsourcing guidelines require institutions to identify, assess, monitor, manage, and report all risks associated with outsourcing of critical functions, as well as to protect customer data across the whole institution, including the outsourced functions. In addition, institutions must develop appropriate plans for the exit from outsourcing arrangements of critical functions and ensure competent authorities remain able to effectively supervise institutions.
An outsourcing policy is a set of guidelines and procedures for an organisation to follow when engaging with third-party service providers. It outlines the criteria for selecting vendors, the contractual terms and conditions, and the expectations for managing the relationship. The policy should also identify the risks associated with outsourcing and the measures taken to mitigate them.

Monthly research, case studies and practical guides you won't find anywhere else.
Join thousands of security managers turning their TPRM programmes into success stories.