How to Manage Emerging Supply Chain Threats
When new vulnerabilities are discovered and threats emerge, organisations have to quickly figure out to what extent their supply chain is affected.


Emerging threats are unpredictable. In cyber security, we’re used to things de-railing our productive workday plans. When something needs dealing with, it needs dealing with. It’s how we deal with it that will make the difference between slight inconvenience and major incident.
So you’ve just been made aware of a new emerging cyber threat, whether that’s a technical software vulnerability...

...or a changing political landscape,

you need to act quickly.
As responsible security professional, you check your internal position: your asset register, network diagram, a few conversations with key people in the business to understand how vulnerable you are and what you can do to mitigate. You understand the extent of your exposure, you make a plan, start actioning and present back to your team. Sorted. Then you’re asked a dreaded question: Any exposure through our supply chain?
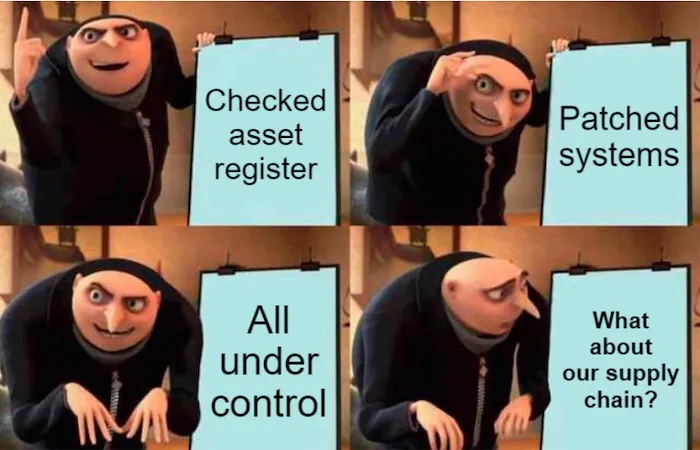
Getting accurate, timely information about how vulnerable your supply chain is to a specific threat is notoriously difficult. In most cases, this particular threat is not something you or your suppliers were thinking about yesterday. Your suppliers have spent the day scrambling around to figure out their exposure, just like you have.
At the moment, for the vast majority of security teams, this effort goes something like:
Meanwhile, the attackers are filling their boots, exploiting the situation left, right and centre.
No wonder cyber crime is such a lucrative business if this is the best kind of agility we can muster up in our defence.
Organisations are now so interconnected and dependent on each other that we need to start taking down some of those human, bureaucratic barriers that prevent an effective response. We need to start making meaningful connections between security teams in supplier-client organisations before an incident happens. We need to start sharing information about IT infrastructure and network activity with trusted partners as a daily norm so that when sh*t hits the fan, we can deal with it quickly and effectively.
The community we’re building at Risk Ledger is enabling these connections and starting to blur the lines between third party risk management and operational security in the supply chain.
The image above shows the interconnectedness of organisations using Risk Ledger for their supply chain security. Each dot is an organisation, with a security team sat behind it maintaining their control profile and collaborating with security teams in client and supplier organisations to better defend as one.
Risk is broader than just cyber. It includes digital, operational, regulatory, and reputational issues. NIST SP 800-161 makes it clear: effective supply chain security means managing confidentiality, integrity, and availability across all supplier tiers.
Do Now: Map your supplier ecosystem beyond Tier 1. Start identifying where data, access, or service delivery dependencies exist.
Do Next: Build a cross-functional risk register that includes non-cyber risks (e.g. geopolitical, legal, ESG) and update it quarterly.
Waiting for disruption is expensive. Modern supply chains need predictive capability and rapid response capacity. Moody’s and Panorays both flag the performance gains of continuous risk insight.
Do Now: Introduce near real-time alerts for known vulnerabilities in your critical suppliers.
Do Next: Move to a continuous monitoring platform that tracks threat signals and cyber hygiene trends across your supply chain.
Spreadsheets and annual questionnaires don’t cut it anymore. Data-led decision-making now means external threat intelligence, shared metrics, and visibility into critical supplier systems.
Do Now: Trial a cyber risk rating tool for your top 10 suppliers. Prioritise those supporting sensitive services.
Do Next: Integrate third-party risk data with your internal SIEM or GRC tooling so supplier risk feeds into enterprise-wide decision-making.
Supply chain and security are still too siloed. That gap slows response and leaves risk unowned. Collaboration needs to happen at the planning stage, not after an incident.
Do Now: Host a joint risk review with procurement, operations, and security. Focus on shared goals, not just compliance.
Do Next: Embed cyber risk discussions into vendor selection, onboarding, and contract renewal processes.
Resilience isn't just about backups. It's about ensuring you don’t have single points of failure across your supplier base. Early detection depends on visibility and adaptability.
Do Now: Identify your critical suppliers and check for concentration risk: geography, tech stack, or dependency on single vendors.
Do Next: Build alternative supply scenarios and test response plans if key vendors go down. Include suppliers in tabletop exercises.
Third-party risk isn’t just your problem. Your suppliers face the same threats and constraints. We need to treat defence as a shared responsibility, not a procurement requirement.
Do Now: Identify your most critical supplier relationships and open a two-way channel for cyber risk sharing.
Do Next: Join or help build a supplier trust community where control data and threat intelligence can be shared securely and efficiently.
The future will bring smarter attackers and tougher rules. Encryption will shift. Threat actors will use AI. Frameworks like NIS2 and the Cyber Security and Resilience Bill demand greater accountability.
Do Now: Audit your current third-party risk practices against NIS2 and upcoming UK regulation.
Do Next: Develop a roadmap for maturing your supply chain assurance programme using standards like NIST CSF, ISO 27036, or the O-TTPS.
We noticed that clients and suppliers struggled to respond effectively when a new, urgent threat was discovered - so we created a tool to fix this.
Supply chains face a wide range of threats, from cyber attacks and data breaches to regulatory non-compliance and geopolitical disruption. In recent years, cyber risks have grown significantly, with attackers increasingly targeting third-party suppliers as an entry point into larger organisations. These threats include ransomware, compromised software updates, stolen credentials, and inadequate security practices across the wider supplier ecosystem. The impact is particularly serious for organisations operating within the UK's Critical National Infrastructure.
The most serious threat is the compromise of a critical supplier, particularly one with access to sensitive systems or data. These suppliers are often overlooked in traditional assessments, making them an attractive target for attackers, including nation-state actors. As these incidents become more frequent and sophisticated, the UK and other governments are moving to strengthen national cyber resilience, placing increased responsibility on organisations to manage supply chain risks effectively.

Monthly research, case studies and practical guides you won't find anywhere else.
Join thousands of security managers turning their TPRM programmes into success stories.